Everything you need to know about the WireGuard VPN Protocol
“Compared to horrors that are OpenVPN and IPSec, WireGuard VPN Protocol is a work of art”
– Linus Torvalds
Said by the great man himself, the inventor of the Linux Operating System.
Since it hit the scene in early 2018, the whispers about WireGuard have been getting louder. In this guide we are going to really dig into what WireGuard is all about, flip the hood and look at some of the technical stuff, whether it’s safe to use and what VPN companies use it.
As well as look at how it matches up with Open VPN, the controversy of why WireGuard may not integrate well with some company’s zero logs policy, and whether it really is the protocol of the future making OpenVPN and IPSec obsolete.
What is a VPN Protocol?
Quick Navigation
Your VPN connects from your device to a VPN server to send and receive data. That connection is carried out using a VPN protocol.
This connection is encrypted and secure to ensure that no one apart from your device and the server can decrypt and read your data.
You can find out more about the pros and cons of each individual VPN protocol in our in-depth guide here (LINK)
What is WireGuard?
Wireguard is an open-source VPN protocol that is faster, cleaner, and simpler to use than OpenVPN. Using more advanced cryptography.
The protocol is cross-platform and the case is used on Linux, Windows, and IOS.
It’s a new generation of the protocol that is pegged to replace the increasingly antiquated IPSec and OpenVPN protocols which are currently the industry standard for secure and encrypted connections.
First released in 2018, WireGuard has been met with industry praise mixed with a healthy dose of skepticism as many waits for it to formally release a stable version 1.0. Designed by Jason Donenfield the founder of Edge Security, and currently supported by several large VPN companies including Private Internet Access and Mullvad.
You can find full documentation at https://www.wireguard.com/
The Technical Stuff?
What makes WireGuard so good?
So, what is all the fuss about, considering that it still doesn’t have a stable version released. Well apart from the high praise it has received from technology titans like Linus Torvalds there are 5 strong reasons why companies eagerly anticipate a stable release:
1. Smaller Code Base
Open VPN – 600,000 lines of code
IPSec – 400,000 lines of code
WireGuard – 4,000 lines of code
Over time OpenVPN and IPSec have become increasingly bloated as they merge other protocols into their codebase. OpenVPN is merged with OpenSSL and IPsec with Strong Swan and XFRM.
From a non-technical standpoint, think of a codebase like the number of pieces of a puzzle. The greater the number of pieces the more difficult it is to find bugs, fix faults and update the software.
WireGuard’s much smaller code base, which was written from the ground up by Jason Donenfeld has a wide number of advantages.
First, when it comes to being an open-source piece of software to be checked and audited, a single developer could run through WireGuard’s entire codebase in a few hours as opposed to days and weeks it would take for Open VPN and IPSec.
Secondly, a smaller code base gives what WireGuard’s website calls a “smaller attack surface.” The less code there, the smaller the chance of a mistake or a vulnerability that could be taken advantage of by a third party.
Lastly, less code means more speed. If you don’t have tonnes of additional bloat, then the program runs faster. If the existing code has been optimized as per the user’s needs. Many developers have long been frustrated with OpenVPN which is littered with code that no longer works, meaning they need to design custom scripts.
For large companies, the smaller code base is incredibly compelling. When you have thousands of clients connecting and disconnecting, fewer places for glitches means faster and smoother connections. OpenVPN has often gained critics for the number of times the “tunnel” either crashes or stalls.
2. Speed
Wireguard offers a faster throughput of data (the amount of data that can be transmitted through the protocol) as well as a lower latency (the delay between a message being sent by your application and received by the server)
OpenVPN is the industry standard for VPN protocols, it is one of the most secure but also the slowest.
Throughput (Mbps)
Latency (Ms)
Source: https://wirevpn.com/
Tests by WireGuard shows it can transmit four times as much data per second, with a third of the latency. When you multiply that over time it becomes a game-changer.
Tech Savvy: The software itself resides within the kernel, which means its much faster-making network connections and works seamlessly hopping between IP addresses as well as moving between 4G and Wi-Fi. As opposed to OpenVPN which switches between the kernel and the userspace.
When you put all this together Wireguard offers monumental upside in terms of speed based upon its design, where it resides in your device and its proprietary connection protocols.
Also, worth noting that the connection speed when starting the handshake is phenomenally faster on WireGuard than Open VPN. Try 1 second vs 8 seconds. A connection that is 8 times faster, also means it’s easier for you as a VPN client to switch servers quickly.
3. More Secure Algorithms
WireGuard also comes with its own encryption and proprietary keys. OpenVPN and IPSec use older keys, which are highly secure. But some would argue this is unnecessary.
WireGuard supports a maximum length of 256-bit keys, and OpenVPN can use a 4096-bit key.
Great! You say it’s more secure. Well considering a 256-bit key would take longer to brute force than the known age of the living Universe. A 4096-bit key sounds like overkill.
Complexity has its limits when it comes to usefulness. These more complicated algorithms also slow down connection speeds. This contributes in part to OpenVPN being 4 times slower than WireGuard. As they use ridiculously long keys!
WireGuard uses the following algorithms:
- ChaCha20 for symmetric encryption, authenticated with Poly1305, using RFC7539’s AEAD construction
- Curve25519 for ECDH
- BLAKE2s for hashing and keyed hashing, described in RFC7693
- SipHash24 for hashtable keys
- HKDF for key derivation, as described in RFC5869
The short version is that they are secure and much faster. In the event you are incredibly paranoid that someone could crack your key, you can use a PSK (Pre-Shared Key)
These simpler algorithms also mean simpler handshakes. Because SSL Encryption for IPSec and OpenVPN is “agile” it means every time a handshake occurs there is a lot of moving parts to match up.
With WireGuard in the event of an attack or breach, you just release a new version of the algorithm and keep a static connection. Reducing time and complexity. You don’t need to keep any old settings between client and server. Just start again.
4. Better Performance
When you combine all the above, from the smaller code base, simplified connections, quicker connection time and proprietary algorithms you get a protocol that gives a future performance.
Also, unlike OpenVPN, WireGuard has been future-proofed for IPv6 as well.
WireGuard is also specially modified for phones which hope between 4G and Wi-Fi, promising a better battery life for devices, better roaming support, more reliable and faster connections as well as faster reconnections when the tunnel is dropped, or the server connection is changed.
5. Ease of Use
More from a developer’s side, OpenVPN can be a nightmare to set up yourself. WireGuard, on the other hand, promises an easy and simple connection you can set up yourself in an afternoon. Not for the faint-hearted but still a big improvement on the existing protocols. This will also help companies when and if WireGuard is distributed on a mass scale. Including fewer server loads, better latency, and fewer dropped connections in theory.
ReviewVPN cannot attest to the legality, security and privacy of the applications discussed on this site. It is highly recommended that you use a VPN service while streaming or using Kodi. Currently, your IP 216.73.216.114 is visible to everyone and your Browser is being tracked by Advertisers & ISP Provider. Here are the main reasons why you must use a VPN: A VPN works be replacing your ISP-assigned IP address and creating an encrypted tunnel. We recommend the no log service offered by IPVanish. It works well on a Firestick and offers the fastest possible speeds.
YOUR INTERNET ACTIVITY IS BEING WATCHED
Install Surfshark on Firestick
Is it Safe to Use?
That is highly debatable. For all the hype around WireGuard, the development team has stated it’s not ready for production:
“WireGuard is not yet complete. You should not rely on this code. It has not undergone proper degrees of security auditing and the protocol is still subject to change. We’re working toward a stable 1.0 release, but that time has not yet come.”
Link: https://www.wireguard.com/#work-in-progress
VPN providers that are using WireGuard must be bleeding edge and keeping up to date with the developments the team is making as they progress towards a stable release.
Judging by the length of their to-do list (https://www.wireguard.com/todo/ ) it seems unlikely this is going to happen anytime soon, but there is a sense of growing anticipation that they are moving towards a release date.
However, as a piece of code, it is safe to use, it just needs to be integrated by professionals who can adjust to a changing codebase. Most of the companies out there are using the API for testing purposes which is separated from their OpenVPN Servers.
The WireGuard codebase is open source so you can also play around with it at home and try and set up a WireGuard server yourself.
What VPN’s Currently support WireGuard?
Currently, there are a limited number of VPN providers that use the WireGuard protocol, the number is growing but is still short:
- Mullvad: Probably the biggest VPN provider using WireGuard right now which supports both OpenVPN and WireGuard (https://mullvad.net/en/what-is-vpn/ ) around since 2009 with a great record for privacy based in Sweden
- IVPN: Founded in 2009 and based in Gibraltar. They have been using WireGuard since 2018 and also supports its development financially, but the announcement on their blog does carry a strong risk message
“WARNING: The WireGuard protocol is currently under heavy development and should be considered experimental. Currently, we do not recommend using WireGuard except for testing or in situations where security is not critical. Our Wireguard VPN servers are separate from our OpenVPN servers to ensure no security risks. We welcome all customers to begin testing, simply select the protocol from within the IVPN client.”
-
- Azire VPN: Founded in 2012 and based in Sweden. They have been running WireGuard for some time. (https://www.azirevpn.com/wireguard ) though they reiterate its in testing, they say they are hopeful and support the project
- WireVPN: The first provider started in 2018, which is entirely based around WireGuard, based in Estonia. The VPN service is still in Beta (https://wirevpn.com/ )
As you can see due to the lack of a stable version of WireGuard, the only companies willing to take the risk are small independent, and cutting-edge VPN providers.
What About Bigger Providers?
PIA: Private Internet Access contributed to the funding for WireGuard’s development. Since September 2018, they have posted in a blog that they are excited about the progress the team has made, but will wait for a stable release
The big players like Surfshark and ExpressVPN have not spoken publicly about Wireguard with Private Internet Access (PIA) the biggest VPN to even nod in their direction. This comes as no surprise as PIA has always been the most vocal and transparent to freedom and privacy online.
BUT, recently NordVPN released NordLynx which uses WireGuard, and they’ve found a way to make it stable to use:
“We needed to find a way for the WireGuard protocol to work without posing a risk to our customers’ privacy.
And we found it. We developed something called a double NAT (Network Address Translation) system.
To put it simply, the double NAT system creates two local network interfaces for each user. The first interface assigns a local IP address to all users connected to a server. Unlike in the original WireGuard protocol, each user gets the same IP address.”
This goes a long way to addressing one of the key concerns we cover later. That WireGuard may compromise the company’s zero logs policy due to the nature of the way it connects.
It looks like WireGuard is that one step closer to going mainstream. NordLynx is currently only available for Linux users.
Why Not Use OpenVPN?
For now, OpenVPN remains the industry standard for all major VPN companies.
Originally released in 2001, Open VPN is now 18 years old, a lot of newer versions of the protocol have been ported from OpenVPN like DD-WRT and Soft Ether VPN.
Over 500,000 lines of OpenVPN’s codebase are taken up by its use of OpenSSL, as well as authentication being certificate-based rather than key-based.
OpenVPN also has the advantage of being able to run over UDP and TCP ports as well as 256-bit encryption run through a security protocol hybrid of SSL and TLS.
OpenVPN has its drawbacks due to the legacy nature of the codebase which has expanded over time. Also, in part by the reticence of large companies to invest in creating better protocols and instead relying on what exists.
The software currently works on almost all platforms including more obscure large-scale architecture platforms like Solaris, FreeBSD, and QNX.
The reason why companies are getting so excited about WireGuard is that it seems to offer a faster, simpler, and more reliable connection with more data being transferred at a time, which will significantly save costs on servers as well as increasing the user experience for clients.
WireGuard vs Open VPN?
So, when we put the young pretender of WireGuard against the established old guard of OpenVPN how do the two match up?
Performance
Though WireGuard has been shown to get better throughput and less latency. Open VPN still outperforms because it’s stable.
This stability comes at the price of speed. This comes down to OpenVPN being used in both user space and kernel space, whereas WireGuard operates only in kernel space.
WireGuard clearly outperforms OpenVPN on both fronts but has yet to present a stable version that can be tested on a large scale.
Security
OpenVPN is used as an industry-standard because it’s secure. With a maximum length key of 4,096 bits using AES and RSA encryption. Many argue this is too much.
Even 128-bit keys are yet to be broken.
WireGuard offers new and innovative encryption in the form of ChaCha 20 and Curve25519 amongst others.
WireGuard also does not use parsers, so is not susceptible to parser bugs, as well as a more modern cryptographic primer with a smaller attack surface due to the size of the code base.
Having said that, no one yet has come forward with a useful vulnerability that can be exploited in OpenVPN, it may be old, but it works.
Ease of Use
From a company and development perspective, there are strong hopes for WireGuard to offer a Window’s client which would allow it to integrate with modern services. Again, this owes to the much smaller codebase.
WireGuard is also more modern in its approach in terms of scrum development by offering version control instead of Open VPN’s certificate-based protocol. This certificate makes OpenVPN more agile but slower.
Version control allows WireGuard to be faster meaning better connection speed, and easier to configure for a wide range of devices and operating systems.
Trust
OpenVPN wins hands down for trust, simply because of the number of eyes that have run over the code. Everyone from Surfshark to the NSA has been over their substantial code base with a fine-tooth comb.
This means more security in adoption and less likelihood of vulnerability.
Again, WireGuard being 100 times smaller, can be audited and understood at a technical level much more quickly.
So Why Weren’t We all using WireGuard Now?
With such a strong case for WireGuard, why aren’t we all using it now?
No Stable Version
The biggest reason is there is still no stable version, nor has Jason given a date for when this could be released, since all the hype in 2018, there hasn’t been a peep since.
But the release of NordLynx by NordVPN is an enormous step towards viability on a mainstream scale, but they really need a Window’s version to make the breakthrough.
Privacy Concerns
In 2018 various companies raised concerns about privacy.
As WireGuard does not use dynamic address management for IP addresses, it needs a fixed client address. This makes the possibility of a client’s original IP being leaked a real possibility.
The last IP a user connected to would need to be saved to allow the WireGuard protocol to work.
The recent release of NordLynx using a Double NAT connection to enable anonymity and no IP logging is intriguing and exciting as potentially the biggest VPN provider has found a way around this problem, though the tool was only released for Linux users at the end of July 2019.
New and Untested
Many companies stick to OpenVPN because it’s reliable. The VPN industry is cutthroat and even a little dip in service could cost a company millions in lost subscriptions.
Though Mullvad and others seem to have used WireGuard successfully for some time without complaint, and WireVPN shows that some people feel confident enough in the protocol to form a company around it.
Limited availability
Currently, the number of companies that offer WireGuard is limited, but that list is sure to grow with Surfshark entering the fray. Expect 2019 and 2020 to see increased adoption of WireGuard and potentially the release of a stable version and even a Window’s client
WireGuard the Protocol of the Future?
Honestly, it seems a case of when rather than if.
On paper, WireGuard wins almost every single battle with OpenVPN which has served us well since 2001.
Surfshark release and PIA’s support mean that WireGuard just needs to get a stable version out with clients that can be tested on a commercial scale.
WireGuard has the promise to change the VPN industry forever. More reliable connections and speed are what the 21st century needs.
Note: For more information about Surfshark, please read our Surfshark Review.
How to Install Surfshark VPN on Firestick
If your Firestick still has the older interface, read this article to learn how to update it: Update Firestick Interface.
Follow our screenshots below to install the SurfShark VPN app on your Fire TV stick.
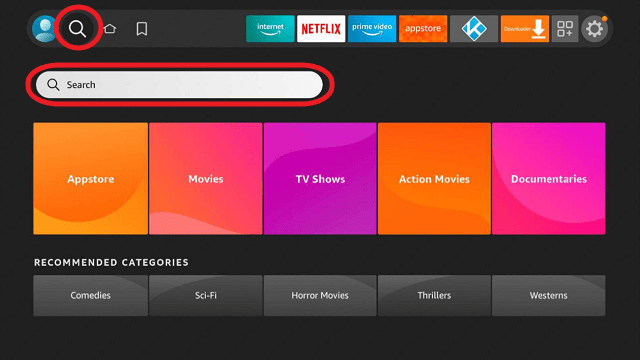
1. Go to the Home screen of your Firestick.
2. Navigate towards the Find tab. Press the Search button from the resulting dropdown.
3. Type in the keyword of SurfShark and select from the suggestions that will appear.
4. Click the official SurfShark icon from your search results.
5. Press the Download (You own it) button.
6. The SurfShark VPN installer will download on your device.
7. SurfShark VPN’s app will automatically install itself on your Fire TV stick.
8. Press the Open button after completing SurfShark VPN’s installation process.
9. Please wait for the SurfShark VPN to load its user interface.
10. You can now log in with your SurfShark VPN account credentials.
Learn more about Surfshark and Grab the Best Surfshark Deal Now!
Install Surfshark on Firestick
For more VPN discounts, go to ReviewVPN Deals and purchase the best VPN for you.
Click here to get the lowest price on Surfshark through our exclusive limited-time offer.