Overview
Do you know your IKEv2 from your SSTP? How about your metadata from your botnet? The world of VPNs is full of technical terms. We’ve put this glossary together to explain all those pesky technical terms and turn you into a VPN expert.
Security Protocols
A VPN secures your connection by encrypting your traffic between your VPN client (mobile/web application or browser extension) and your VPN’s server. To do this, they use a security protocol to encrypt and decrypt your data. Imagine your data being put in a box that is locked and unlocked using a unique key.
Let’s cover the most popular types of security protocols
PPTP
Point to Point Tunnelling Protocol. This protocol creates a tunnel between two points for your data. The oldest and fastest security protocol. Also, the least secure and commonly paired with another protocol to increase security.
IKEv2
Internet Key Exchange version 2. The newest security protocol originally released in 2005. Specifically designed for information exchange between mobile devices. Supports multiple ciphers and has a high-security standard as well as fast speeds. Widely seen as one of the most secure security protocols.
OpenVPN
The industry standard. This is an open-source commercial software that is used by almost all VPN providers. The software works by creating a secure point-to-point connection using OpenSSL to encrypt data and keys and then be authenticated by the server. Has a custom security protocol using SSL/TLS.
L2TP
Layer Two Tunnelling Protocol. The new and improved PPTP. It is a specific tunneling protocol and does not provide encryption. Often used with other security protocols like IPsec which encrypts the data that L2TP transmits. This protocol is solely used to transmit and receive data, but not encrypt it.
SSTP (Windows Only)
Secure Socket Tunnelling Protocol is used only on Windows Computers and is known to be significantly more secure than PPTP. Acting very much like Open VPN, the protocol transmits and encrypts data using SSL/TLS and gives you the ability to access remote servers which also use the SSTP protocol.
YOUR INTERNET ACTIVITY IS BEING WATCHED
ReviewVPN cannot attest to the legality, security and privacy of the applications discussed on this site. It is highly recommended that you use a VPN service while streaming or using Kodi.
Currently, your IP 216.73.217.148 is visible to everyone and your Browser is being tracked by Advertisers & ISP Provider.
Here are the main reasons why you must use a VPN:
- Your activities are hidden from your ISP, the government, and from the apps you are using.
- You can access additional movies and TV streams.
- ISP attempts to throttle are thrwarted thus reducing buffering issues.
- Geographically restricted content like Netflix and Hulu can be unblocked.
A VPN works be replacing your ISP-assigned IP address and creating an encrypted tunnel. We recommend the no log service offered by IPVanish. It works well on a Firestick and offers the fastest possible speeds.
VPN
Virtual Private Network. A service that provides privacy and anonymity by encrypting your data online and protects your identity by masking or changing your IP Address which reveals your true physical location.
Kill Switch
Built into a VPN client. If for any reason your VPN stops working, this switch will ‘kill’ your internet connection until your VPN restarts. This is to prevent your true IP from being seen.
Simultaneous connections
The number of devices which can connect to your VPN at the same time. Using the same or different IP addresses.
Tor
The Onion Router. A system of decentralized nodes based on people’s computers. Known for anonymity as it masks your connection by bouncing your data through different encrypted connections. Making your browsing practically untraceable.
VPN Protocol
The rules determine the connection between your VPN client and server. Which could include connection protocols, encryption, and decryption as well as which server to connect to.
VPN Server
A programme that grants access to your provider’s network. Allowing you to appear in different physical locations and change your IP. This is where your data is decrypted going out and encrypted coming in as you browse online.
VPS
Virtual Private Server. A virtual machine where your data is hosted. Rented from an internet hosting service, it can be based anywhere in the world. As opposed to a physical server based at your property or close by.
Warrant canary
A method VPN providers use to inform their users if they have been served a subpoena or legal summons by a law agency. If the canary if updated or present on the site, then that means the company is NOT under investigation. When the canary disappears or stops being updated, then it signals the company is part of a criminal investigation. This is to circumvent laws around informing users that they are under investigation, by clearly stating when they aren’t under investigation instead.
WEP
Wired Equivalent Privacy. The security protocol used for Wi-Fi connections. Giving the same level of security as a wired LAN internet connection.
WPA2
Wi-Fi Protected Access 2. The encryption and certification protocol for most Wi-Fi connections.
TLS
Transport Layer Security. The encryption protocol for any form of communication over a computer network. Preceded by the now deprecated SSL (Secure Socket’s Layer) This protocol is used to secure many everyday habits like email, text messages, and internet browsing.
SmartDNS
An alternative to a VPN. With a few key differences. DNS stands for Domain Name System. They assign names and IP addresses to websites. When a website like Netflix receives a request from you, it uses your DNS to identify your location and attributes. A SmartDNS shows you as connecting from a different country but doesn’t change your IP, unlike a VPN. Also, it does not encrypt your data or allow you to unblocked censorship content. Only useful for accessing geo-secured sites.
AES
Advanced Encryption Standard. Originally known as the Rijndael cipher. A global encryption standard to secure data. Used by the US government and military and now as industry standard for VPN’s. The cipher comes in 128,192 or 256 bits. Commonly you will see that your data is secured using a 256-bit AES encryption. This level has never publicly been broken or ‘brute force’ decrypted.
Proxy
A proxy server acts as a bridge between two parties. Your traffic passes through a proxy before connecting to your target website. The proxy server can alter your data by encrypting it, or modifying the data based upon your request and the function of the proxy.
Ping Time
Used as a measure of internet speed. This is the time it takes for your connection to get a response once it sends a request. This is determined by the speed of your cable connection and the speed of the website’s server.
Packet
A packet is a unit of data. Everything you do use a computer and any form of data involves data packets. This is how you send requests and receive information and requests online.
OpenSSH
Secure Shell Protocol. OpenSSH is used to secure a channel over an unsecured network. This is the open-source alternative to SSH. Used generally to secure communication between a client and server.
Meta Data
Data about data. The metadata in a packet tells the computer what type of data it is receiving. The metadata of an email for example would tell you there is text, headers, formatting and a sender and receiver address.
Man in the middle attack
When data is sent and received between two points, it goes through a man in the middle. This could be a proxy server for example. A man-in-the-middle attack happens, when an attacker intercept data between two points pretending to be a server. Think about someone listening in to your phone call. These attacks can be avoided using an encryption system that requires endpoint verification. So, someone cannot pretend to send and receive data without the appropriate encryption key.
Wardriving
An attacker will be in a moving vehicle. Using a phone or laptop they will search out and map Wi-Fi networks. This map of networks can then be used as a GPS system where a person is tracked based upon the relative strength of internet networks at their location.
Botnet
A botnet is a series of computers or internet-connected devices that are linked in a network and used to run a bot. Used for hacking practices like a DDOS attack (distributed denial of service attack) Here a botnet is used to flood a website with thousands of requests per second overloading the website’s servers and causing it to crash.
Brute Force
A brute force attack is commonly associated with breaking passwords and encryptions. A powerful computer is used to go through every single combination to find the right one. For example, a 4-digit pin number has 10,000 possible combinations. Banks stop someone from being able to brute force a pin number by limiting you to 3 possible attempts before blocking the card. Modern 256-bit AES encryption has been found to be impervious to brute force attacks, purely due to the number of combinations that need to be attempted. You would need to try 2 to the factor of 256 attempts minus 1 bit. Even the best supercomputers today would take trillions of years to brute force a 256-bit AES key.
NAT
Network Address Translation. A method used to mask a computer’s true IP address. This method of remapping an IP changes the IP metadata in your data packets to show it coming from a different IP address
Log
Commonly seen in a VPN provider’s ‘no-log policy, a log is a record of your usage of a service. This could include your original registration details like name, address, and a credit card or payment. When using the service, a provider can log your original IP address, servers used, browsing history and time, data uploaded and downloaded as well as anything else you do while connected to their service.
IPv4
The fourth revision of the Internet Protocol. An IP is used to identify the device and location you are browsing from. Essentially an internet address book. New IPv4 addresses are no longer being assigned as they ran out. Originally the protocol only allowed for 4 billion addresses as it only used a 32-bit address protocol. New addresses use IPv6.
IPv6
The sixth revision of the Internet Protocol. IPv6 was introduced as we basically ran out of IP addresses. These addresses are also considerably more complex, easy to use, and faster than IPv4 addresses to adjust for technological and network advancements.
IP lead
IP leads are a form of tracking used by companies for their marketing. As well as malicious parties who want to trace back people’s IP addresses. An IP address can be used to trace where you are from and aggregate it alongside other data used to show what your browsing habits are, as well as your preferences.
IP Address
An IP address is a unique address that is specific to your internet connection. It allows a fixed point for your data to travel to and from. Like a map. You go from one IP to another and your server needs to know where to send and receive data. IP’s can be static (the same constantly) or Dynamic (changing) as well as Public or Private.
Great Firewall
China’s internet censorship project and system of technology used to monitor traffic within its borders as well as censor content it deems to be unacceptable. Acts principally to ‘protect’ the China public from foreign companies and information and nurture domestic companies as well as propagate nationalistic propaganda which is pro-government.
GeoIP / Geo-spoofing
Your IP address will reveal the country that you are connecting to the site from. Based on your location a website’s server could block or alter the content. Commonly used by media sites like Netflix as well as e-commerce and comparison sites that may change prices based upon your location. Geo-spoofing is used by VPN providers to change the location of the IP you use to visit a site. Essentially showing you are browsing from a country that allows you to access the site.
5 Eyes, 9 Eyes, 14 Eyes
A series of countries have an international agreement to share intelligence and information.
Started with the 1941 Atlantic Charter where the UK and USA agreed to intelligence share during World War 2, extended to the 5 eyes with New Zealand, Australia, and Canada.
The 9 eyes consist of the above 5 countries and Norway, The Netherlands, France, and Denmark.
The 14 eyes consist of the above 9 countries and Sweden, Spain, Italy, Belgium, and Germany.
The different groups are also thought to reflect the level of information shared between the countries. With the 14 eyes perhaps sharing less than the 9 eyes and 5 eyes. As each country also has active operations to spy on each other.
Firmware
Permanently installed software in your electronic device. Recently concerns have been raised that a company may use firmware to also snoop on a person’s habits and even their location.
Malware (Added)
Software designed to intentionally damage your computer or server. Which can be also used to control, monitor, or disrupt usage on that device.
Firewall
Firewalls control the flow of data through a network. Provides security by updating itself to monitor new types of malware and viruses.
Encryption Key
An encryption key is a unique code to unscramble your data. A VPN encrypts your data in a client and then decrypts it in their DNS. This means that only a device that has the corresponding key can see your data.
DNS Poisoning
Also known as DNS spoofing. A healthy DNS routes your traffic to the correct website. A hacker can spoof a DNS and redirect your traffic to a malicious website.
Our Top Rated VPN Service
With all of the VPN services and protocols available today, Surfshark has been our tested and recommended VPN service. It offers first-rate protocols, features, prices, and customer service, among other things.
It employs AES-256-GCM encryption, the most powerful standard available today. Additionally, Surfshark employs the 2048-bit RSA key and the Wireguard protocol’s Chacha20. It also makes use of some of the top protocols now in use, including IKEv2, OpenVPN, and WireGuard. As a result, you can be confident that all data transmission in and out of your device is encrypted while maintaining the fastest speed currently available.
It also has a kill switch in case of an unexpected VPN interruption. Apart from that, the following are some of its standout features:
- Provides 3,200 servers in 100 countries for your anonymity.
- Allows for an unlimited number of devices and simultaneous connections.
- Ensures that no logs are kept when utilizing its service.
- It contains a CleanWeb feature that prevents advertisements, trackers, malware, and phishing attempts.
- To prevent obtrusive cookie consent pop-ups, there is a cookie pop-up blocker.
- IP Rotator that switches the user’s IP address at the selected location every five to ten minutes without cutting off their VPN connection
- Customer service is available 24 hours a day, 7 days a week via live chat or email.
- It has a help center and blog, as well as a channel on YouTube with tutorials and other knowledge bases.
Grab your subscription now!
How to Install Surfshark on Firestick with Screenshots
If your Firestick still has the older interface, read this article to learn how to update it: Update Firestick Interface.
You can download Surfshark directly from the Amazon App store. It will be easy for you to find Surfshark with your Firestick’s Find feature. Refer to our screenshots below.
Follow our screenshots below to install the SurfShark VPN app on your Fire TV stick.
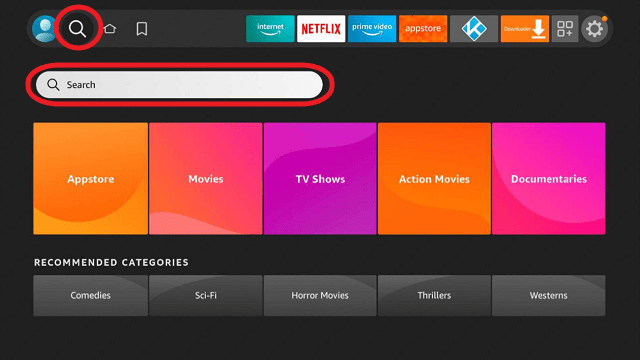
1. Go to the Home screen of your Firestick.
2. Navigate towards the Find tab. Press the Search button from the resulting dropdown.
3. Type in the keyword of SurfShark and select from the suggestions that will appear.
4. Click the official SurfShark icon from your search results.
5. Press the Download (You own it) button.
6. The SurfShark VPN installer will download on your device.
7. SurfShark VPN’s app will automatically install itself on your Fire TV stick.
8. Press the Open button after completing SurfShark VPN’s installation process.
9. Please wait for the SurfShark VPN to load its user interface.
10. You can now log in with your SurfShark VPN account credentials.
Learn more about Surfshark and Grab the Best Surfshark Deal Now!
Install Surfshark on Firestick
For more VPN discounts, go to ReviewVPN Deals and purchase the best VPN for you.
Click here to get the lowest price on Surfshark through our exclusive limited-time offer.