Overview
Quick Navigation
This article will discuss the different types of VPNs.
There are numerous VPN services available on the market today, and they have grown in popularity across major platforms due to the level of protection they provide to their clients. Whichever type of internet user you are, a VPN can significantly improve your online experience and security while utilizing public wi-fi or the internet.
However, there are widespread misconceptions or misinformation about the various forms of VPN. How can you know if you’re using the appropriate VPN for your online activity? That is why this post will enlighten you on the different types of VPNs so you can determine which ones to seek in a VPN service based on your needs and usage.
Moreover, VPNs operate on a variety of different levels, and to select the best VPN for you, you must first understand how they work. So, without further ado, let’s start figuring out the different types of VPNs.
Main Types of VPN
VPN connections come in two types: Remote Access VPN and Site to Site VPN.
Remote Access VPN
VPN is a network technology that provides a secure tunnel over the internet. It enables users to exchange and receive data while remaining anonymous to the rest of the world. There are numerous types of VPN, but one of the most common and widely used is Remote Access VPN.
Remote access is popular with businesses because it enables remote users to connect to network resources located in several places. Establishing a secure encrypted tunnel between sites, it extends the private network to a remote place.
Individual VPNs from major VPN providers such as Surfshark and others are also a form of remote access VPN. These VPN service providers have VPN servers located throughout the world to which you can connect, and each of these distinct servers allows you to select a different location each time you connect.
It’s worth noting that your internet activity will be focused on a single network in this instance. You may be confident in this because when you connect to a certain VPN server, it is the only network through which your internet activity will flow.
Site to Site VPN
Site-to-site VPNs differ in that they connect many networks rather than connecting individual devices. Essentially, this network of sites connects via a secure link. The secure connection enables to transfer and receive of data from any location on the network while encrypting it for security and ensuring its integrity by preventing eavesdropping or tampering.
Moreover, this form of VPN enables you to centralize your organization’s network security policies on several servers rather than managing security on individual systems at remote locations. Site-to-Site VPNs connect numerous network locations, not just between two networks. With that, data can be delivered and received throughout the entire network via a secure network gateway, allowing for simultaneous remote access to various locations.
Furthermore, Site-to-site VPNs safeguard network communication through the use of encryption and authentication. They establish a secure connection that prevents unauthorized access to network traffic.
- Intranet-based VPN: This type of VPN is used in multiple offices within a single company that is connected by a Site-to-Site VPN.
- Extranet-based VPN: This is when a Site-to-Site VPN is used to connect to another company’s office.
What is the main distinction between these two types of VPN connections?
While the types of VPN (Virtual Private Network) have their own set of advantages and disadvantages, the distinction is simple: a Remote Access VPN enables employees to connect to corporate network resources from remote locations such as their homes or while on the go through a single encrypted connection. On the other hand, a Site-to-Site VPN enables networking resources distributed across numerous locations connected centrally by a physical link or an authorized data access channel.
Additionally, a remote access VPN enables users who are not connected to the primary network to securely connect to it via the internet. Site-to-site VPN, on the other hand, is used to connect locations via a secure shared gateway through which all data goes.
Different Types of VPN
Individual / Personal VPN
As the type implies, these are VPN services that are utilized privately or by an individual connected over a private connection. This form of VPN is intended to prevent IP address leaks and data breaches when browsing online material for personal leisure.
Apart from security, there are other advantages to having a personal VPN. The majority of users wish to utilize them to gain access to restricted content. So if you live in a country where certain websites are blocked or you don’t want your ISP to be able to monitor your activity, a personal VPN is regarded as the simplest solution.
Business VPN
This form of VPN is employed by huge corporations since, of course, a corporation requires a dependable VPN service to encrypt all incoming and outgoing data. Apart from that, organizations frequently have confidential files that they do not want anyone to access, which is why they utilize business VPNs. Particularly now that the majority of people are working from home as a result of the epidemic, many organizations have relied on this form of VPN to ensure the highest level of anonymity for file transfers for both employees using remote access and site-to-site VPNs.
Moreover, you may like to read our post on the best VPNs for business. So you could learn more about which VPNs are suitable for businesses, as this sort of VPN offers a variety of unique features and options.
Free VPN
What’s great about modern technology is that you can even obtain free VPN access. While these free VPNs have fewer features than personal and business VPNs, it’s worth noting that they provide a free VPN service for people on a budget or who are just starting with VPN exploration and use.
Meanwhile, some personal and business VPNs provide a free trial or a money-back guarantee to compete with free VPN services. Alternatively, they offer both free and premium VPN options, allowing users to easily upgrade from the free to the premium plan.
You can read this article to learn more about free VPNs as well as a list of providers who offer free VPNs.
YOUR INTERNET ACTIVITY IS BEING WATCHED
ReviewVPN cannot attest to the legality, security and privacy of the applications discussed on this site. It is highly recommended that you use a VPN service while streaming or using Kodi.
Currently, your IP 216.73.216.234 is visible to everyone and your Browser is being tracked by Advertisers & ISP Provider.
Here are the main reasons why you must use a VPN:
- Your activities are hidden from your ISP, the government, and from the apps you are using.
- You can access additional movies and TV streams.
- ISP attempts to throttle are thrwarted thus reducing buffering issues.
- Geographically restricted content like Netflix and Hulu can be unblocked.
A VPN works be replacing your ISP-assigned IP address and creating an encrypted tunnel. We recommend the no log service offered by IPVanish. It works well on a Firestick and offers the fastest possible speeds.
The Best VPN for All Possible Usage
Now that we’ve covered a variety of aspects of VPNs, it’s important to determine which one is truly the best when it comes to the various criteria that contribute to the best VPN service.
Surfshark
Surfshark is one of the most popular VPN services and has been the best due to its no-log policy, fast internet connection, unlimited number of simultaneous connections, numerous protocols used, end-to-end encryption, and other security measures. It has been preferred by many because it ensures the highest protection when it comes to safeguarding and encrypting one’s internet activity. Moreover, it features the best functionalities of a VPN such as the following:
- 3,200 VPN servers in 65 worldwide locations ensure that you’ll always have access to the internet for your daily activities.
- Utilizes military-grade AES 256-bit encryption, the same as that employed by the US government and banks to provide unbreakable end-to-end encryption.
- WireGuard, IKEv2, OpenVPN, L2TP, IPSec, and PPTP protocols are used to ensure a secure connection while keeping the greatest possible speed.
- Zero logs and no IP address leaks are guaranteed.
- It includes a kill switch that automatically disconnects your device from the internet in the event of an unexpected VPN connection interruption.
- Compatible with a variety of different operating systems, including Windows, macOS, iOS, Android, Fire TV, Linux, and Chrome OS.
- Allows you to circumvent censorship and geo-restrictions through the connection provided by Surfshark 65 locations, allowing you to stream content from anywhere in the globe.
- Secure all of your devices with Surfshark’s unlimited number of simultaneous connections, which can be used for both personal and business use.
- Take advantage of unlimited bandwidth to stream and download all movies, TV series, and other media available on the internet.
- There is a 30-day money-back guarantee if you want to terminate your subscription for various reasons.
Install Surfshark on Firestick
How to Install Surfshark VPN on Firestick
If your Firestick still has the older interface, read this article to learn how to update it: Update Firestick Interface.
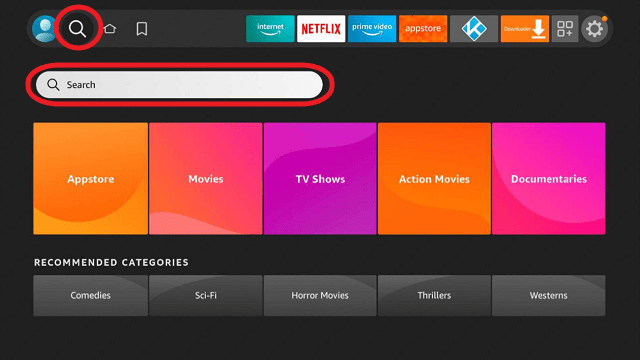
You can download Surfshark directly from the Amazon App store. It will be easy for you to find Surfshark with your Firestick’s Find feature. Refer to our screenshots below.
1. Go to the Home screen of your Firestick.
2. Navigate towards the Find tab. Press the Search button from the resulting dropdown.
3. Type in the keyword of SurfShark and select from the suggestions that will appear.
4. Click the official SurfShark icon from your search results.
5. Press the Download (You own it) button.
6. The SurfShark VPN installer will download on your device.
7. SurfShark VPN’s app will automatically install itself on your Fire TV stick.
8. Press the Open button after completing SurfShark VPN’s installation process.
9. Please wait for the SurfShark VPN to load its user interface.
10. You can now log in with your SurfShark VPN account credentials.
Learn more about Surfshark and Grab the Best Surfshark Deal Now!
For more VPN discounts, go to ReviewVPN Deals and purchase the best VPN for you.
Other VPN Options for Businesses
Perimeter 81
Perimeter 81 is another well-known VPN for business. It provides industrial-strength security features that safeguard your network from advanced threats and targeted network attacks. Apart from that, it offers blazing speed for a minimum subscription fee of $8 per month for five users. It uses AES-256-bit bank-level encryption and supports the OpenVPN and IKEv2 protocols. Moreover, Perimeter 81 is available on a variety of platforms, including Windows, Mac, Linux, iPhone, Android, and Chrome. However, compared to Surfshark, there are few admin logs on their service, and have fewer servers available with 700 servers in more than 36 locations.
Free VPN to Consider
TunnelBear
TunnelBear is a decent free VPN that keeps no logs, has solid encryption, and includes the kill switch, which is the most popular feature of VPN services these days. Furthermore, it employs military-grade AES-256 encryption and SHA-256 authentication, as well as OpenVPN and IKEv2 protocols, making it a viable alternative for a free VPN. However, because it is free, expect it to have fewer features than premium VPNs. As a result, I can say that this VPN is solely suitable for personal usage.
FAQs
What are the two types of VPN connections? (choose 2)
VPNs are classified into two types: remote-access VPNs and site-to-site VPNs. While both types of connections are secure, remote access is provided from a single location, whereas site-to-site connections are gathered from multiple locations.
Which type of VPN is most commonly used today?
Today, the most often used VPN is a remote access VPN. The majority of VPN services use this since it provides individual privacy and is suitable for personal use.
How many types of VPN protocols are there?
There are various VPN protocols available, but WireGuard, IKEv2, OpenVPN, L2TP, IPSec, and PPTP are the most regularly used.
- Wireguard is a new VPN protocol that is faster, stronger, and lighter than previous forms of connection.
- IKEv2 is a protocol that configures the security association or the specific method that encrypts IP packets using IPSec.
- OpenVPN is an open-source virtual private network (VPN) that establishes point-to-point and site-to-site connections.
- L2TP is often used in conjunction with another VPN security protocol to provide a secure VPN connection.
- IPSec encrypts data packets to protect Internet communication across an IP network.
- PPTP is a popular VPN protocol because it creates a tunnel that encrypts data sent between the two devices.
- SSL/TSL establishes a VPN connection in which the web browser serves as the client and user access is restricted to selected applications rather than the full network.
- SSH – creates the VPN tunnel via which the data is transferred and ensures that it is encrypted.
Is VPN safe?
Yes, VPNs are safe. In fact, it gives an additional layer of security to its clients’ activities.
Is VPN legal?
Yes, using and installing a VPN on any device is legal.
Are there free VPNs available?
Yes, there are some free VPNs available such as Tunnelbear, and some VPN providers offer a free trial or a money-back guarantee. However, free VPNs typically offer fewer capabilities than paid and premium VPNs.
Install Surfshark on Firestick
Conclusion
Virtual Private Networks (VPNs) are an important part of any organization’s or individual’s security. VPNs encrypt data at the source, transfer it via an insecure network, then decrypt it at the endpoint.
It transfers data securely over public networks. Keeping it safe from prying eyes, hackers, and other systems that use IP to determine someone’s identity.
However, one needs to be aware of the different types of VPNs. So they can determine which one to use and subscribe to for the safety they require. With that, we’d like to thank you for taking the time to read our article about the different types of VPNs.
We hope we were able to enlighten you on the key differences to search for when selecting a VPN subscription.